Acronym Buster: IT Operations Tools
TLDR: There's a LOT of different tools out there...
Clearly feeling the world was in desperate need of more acronyms, IT operations has well and truly stood up to the plate. Dazed and confused - and with FOMO about to kick in – I thought now would be a good time to write up an acronym buster so I could finally put those woes to bed. That, and I promised my manager I'd publish a new blog before COP.
So, if you don’t know the difference between ITSM and ITSA, or MDM and SIEM for that matter, then this short little article is for you. FWIW, I’ll be using the WYSIWYG to make sure this article really pops. And don’t worry, everything you're about to read is certifiably SFW.
APM: Application Performance Management
Although alphabetical, our starting point is probably one of the most established acronyms on the list.
Conceptually, APM tools focus their monitoring efforts on the end user - a trait that up until recently (technology-wise anyway) was unfamiliar territory. APM tools provide a holistic view for application performance and aim to surface performance metrics that will help remedy application performance faults.
They are usually priced per application and are typically reserved for highly visible or revenue generating apps. They come into their own for actively developed or in-house applications where infrastructure components are largely known, and as such, have been well received within the DevOps community.
Example vendors: Dynatrace, App Dynamics, Stackify and Application Insights
AIOps: Artificial Intelligence for IT Operations
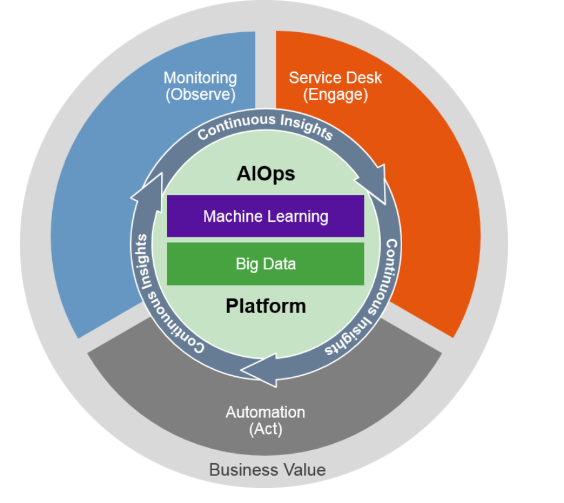
AIOps sees the marriage of two ridiculously hot IT buzzwords come together and form a new breed of monitoring: Big Data and Machine Learning. Fancy.
Like Enterprise Application Monitoring (more on this later), tools of this nature aim to breakdown monitoring silos by aggregating existing data and returning it in a form that is more meaningful to the end user.
As describe by Gartner, AIOps tools tends to aggregate existing observational data (e.g. logs and monitoring data) alongside engagement data (e.g. ticket and incident management software) inside a Big Data platform where Machine Learning capabilities will kick in. The diagram below, inspired by Gartner, depicts how these insights are then theoretically used to provide Continuous Integrations and Deployment insights to core IT functions.
Example Vendors: Moogsoft, Hewlett Packard Enterprise, BMC and FixStream
CM: Configuration Management
Just to add to the confusion, I found a nifty definition for Configuration Management on an APM website - which in this particular incidence stands for the Association of Project Management NOT Application Performance Management. D’oh.
"Configuration management encompasses the administrative activities concerned with the creation, maintenance, controlled change and quality control of the scope of work." - definition courtesy of apm.org.uk
Put simply then, CM tools help IT teams identify, plan and deploy functional or physical changes for IT software projects. And for any actively developed software project, as you can imagine, there will be plenty of code and physical change requests to manage.
Example Vendors: Puppet, CHEF, Saltstack and Octopus
EAM: Enterprise Application Monitoring
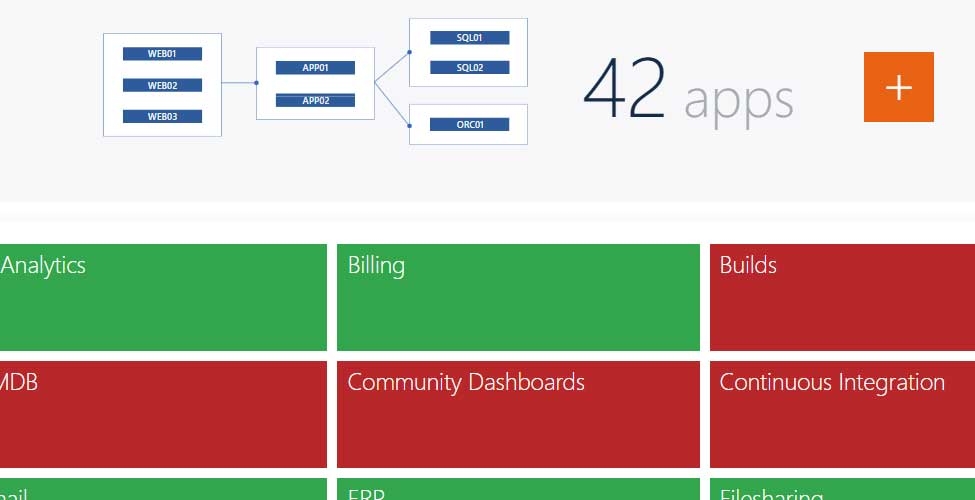
An acronym close to our heart, EAM tools allow you to put all your existing monitoring data in the context of key applications and services – without the need for any new agents, databases or infrastructure.
To put this into context, SquaredUp acts as a presentation layer that sits on top of Microsoft System Center Operations Manager (SCOM), utilizing your existing monitoring agents, so you can map and monitor all your enterprise applications. Not just a select few.
So, like the APM tools we mentioned earlier, EAM switches the focus away from infrastructure and towards applications, and like those funky AIOps tools, EAM makes application performance insights available to the masses.
Example Vendors: SquaredUp
Everything you need to know about APM
ITAM: IT Asset Management
IT Asset Management, sometimes referred to as IT Inventory Management, is the practice of gathering detailed hardware and software inventory data. And whilst this might sound pretty benign, for any large organization this is a mammoth task.
Once gathered this information is typically used to make strategic purchase decisions for new equipment and software. Essentially ITAM tools help IT manage the lifecycle process for all internal IT assets and are typically used by all departments involved in the procurement, reporting and deployment of these assets.
Example Vendors: Freshservice, Samange, Device42 and Asset Cloud
IDM/IAM: Identity and Access Management
Moving on nicely from ITAM, we can now turn our attention to IDM. The contrast between the two is, whilst ITAM is focused on inventory data, IDM technologies keep tabs on who has access to these resources. Helping manage the identification and authorization process for the all the IT assets we mentioned earlier. For that reason. IDM tools typically fall under the remit of IT security.
As put by Gartner, IAM tools are all about giving individuals access to the right resources at the right time for the right reasons.
Example Vendors: Okta, One Logic, SailPoint and Contrify
ITIL: IT Infrastructure Library
Unlike all the acronyms previously covered, ITIL isn’t a tool.
ITIL is a set of detailed practices for IT service management (ITSM) – more on this later – that try to align business needs with IT services. It describes numerous processes, procedures, checklists and tasks that need to be followed in order to demonstrate ITIL best practice. And whilst the onus is on the company to follow this framework, only individuals, not companies, can be ITIL certified.
The rise in popularity of ITSM tools, tools like ServiceNow, can be largely credited to the fact they help organizations adhere to ITIL best practice.
It’s a pretty broad topic, for the purposes of this acronym buster, simply remember that ITIL is a framework for marrying IT services with business needs. More information on ITIL is available via this website.
ITIM: IT Infrastructure Monitoring
Another acronym we’re all too familiar with. As described earlier, SquaredUp’s EAM tooling essentially acts as a presentation layer that sits on top of one of the most powerful ITIM tools around: SCOM. You see, it's thanks to SCOM’s extensible nature that SquaredUp can pull in performance data across your entire technology stack. We just turn existing data into insights.
Without further context, ITIM tools will simply report on the health and availability of IT infrastructure components that reside within internal data centers or are hosted in the cloud.
Centralized monitoring teams that rely on these tools will have a hard time answering how these numbers translate back to business outcomes, identifying priority alerts and finding the root cause for application performance issues. But what they will do is a bloody good job collecting infrastructure performance data.
Example Vendors: Microsoft (SCOM), Solarwinds, Nagios and HP OneView
6 ways you can reduce your MTTR
ITOA: IT Operations Analytics
Bit of a strange one this as, to my knowledge anyway, ITOA essentially serves as a broader category of product. That is to say, an APM tool could rightly be classified as an ITOA tool too. And although lecturers from a previous life would be shaking their head in disappointment, this quote from Wikipedia adds some much-needed context:
ITOA technologies are primarily used to discover complex patterns in high volumes of often "noisy" IT system availability and performance data. Forrester Research defined IT analytics as "The use of mathematical algorithms and other innovations to extract meaningful information from the sea of raw data collected by management and monitoring technologies."
A rather benign definition don’t you think? It’s easy to see how many of the previously mentioned IT tools could also fall under this category.
Example Vendors: Elastic, Splunk, Evolven and SquaredUp
ITSA: IT Service Alerting
According to Gartner, ITSA tools automate the distribution and management of notification messages for intended recipients. Typically, ITSA tooling will integrate with your existing ITOA landscape and serve as the endpoint for managing alerts.
The best ITSA tools will allow users to update their communication preferences so they can receive alerts in their preferred format. Extending will beyond SMS capabilities, ITSA tools will also provide the ability to arrange calls, send pager updates or notify end users via a dedicated smartphone application.
Example Vendors: PagerDuty, OpsGenie, VictorOps and Statuspage
ITSM: IT Service Management
Woah – this acronym buster is dragging on a bit isn’t it? In the interest of speed, if you’re familiar with ServiceNow then you already have a broad understanding of ITSM.
For those looking for a bit more detail, ITSM tools have essentially productized ITIL principles. They help organizations provide a Single Point of Contact (SPoC) between the business and IT – typically the Service Desk – and help IT better manage the lifecycle for all internal IT services.
For clarity, an IT service can be anything from your physical laptop, access to a business application or the ability to use a printer. Any time IT is involved think of it as an IT service provided to the business. The best ITSM tools provide a lot more functionality and play a pivotal role in what goes on behind the scenes, but for the purposes of this acronym buster, this will have to do.
Example Vendors: ServiceNow, Cherwell, Ivanti, and ServiceDesk
MDM: Mobile Device Management
Our penultimate definition! We’re nearly there!!!
MDM is a type of security software that is used by IT to monitor, manage and secure mobile devices used by employees. This could mean anything from configuring equipment to a consistent standard, monitoring hardware performance, tracking ownership or troubleshooting equipment issues from a remote location.
The best MDM solutions will also have functionality in place to manage BYOD (bring your own device) equipment too. Which in most cases translates to giving personal devices limited access to non-sensitive information.
Below is a cool little diagram provided by ManageEngine that neatly summarises core MDM responsibility.
Example Vendors: SOTI, AirWatch, MobileIron, and Microsoft Intune

SIEM: Security Information and Event Management
I know there’s plenty more acronyms I could and probably should cram into this guide, but I’ve got to be honest, I’m running out of steam. And for that reason alone, we’re going to end this acronym buster on SIEM.
At a top-level SIEM technologies combine Security Information Management (SIM) and Security Event Management (SEM) functions into a dedicated security management portal. They aggregate and analyse existing log data, in real-time, so you can fire alerts when suspicious activity occurs.
TechTarget explain that SIEM tools, at the most basic level, will fire alerts when data sits outside pre-established baselines (rule-based), whilst more advanced systems will perform statistical analysis to establish relationships between log and event entries.
Example Vendors: Vetra, Tanium, Symantec and ObserveIT