SCOM 2019: What’s next

"Who doesn't love monitoring?" said no one ever. Well, no one but me. Seriously. I love monitoring, but oftentimes I felt like I was the only one. After 23 years at Purdue University I decided that it was time to change things up, try something new, and start looking to see if monitoring could be fun, interesting, and actually creative for someone other than myself. Surprisingly for me, SquaredUp was also interested in the same thing! Going forward, I'll be blogging for SquaredUp and for myself on a number of topics like SCOM, Azure Monitoring as well as other topics that are interesting to me and I hope, for you too. But first, I want to share all of the goodness the SCOM product team announced at Ignite 2019 for SCOM.
Ignite 2019 is like a HUGE Thanksgiving Day celebration, for five whole days, from sunrise to sunset (and sometimes beyond)! For those of you in the United States, you probably get that reference, but for everyone else, imagine getting your favorite meal. At each meal time. And it's every day… for five whole days! That's how much juicy information was poured out at the Ignite conference. Honestly, it was way too much and the work coma was intense the following week…
That said, one of my favorite sessions from Ignite was the "SCOM 2019 Customer Success Stories and What's Next" session. If you can't already tell, I have a deep passion for monitoring and (love it or hate it) SCOM. In addition to the new features, there were also two customer stories added to the session. While most people are probably only interested in what's coming for SCOM, I'm always interested to hear about what fellow SCOM Admin's are doing with the tool.
Okay, enough babbling, on to the good stuff!
Speakers:
- Vithalprasad Gaitonde, Principal Program Manager, Microsoft
- Hitesh Sharma, Senior Program Manager, Microsoft
- Petr Volprecht, Global Service Owner for SCOM, SAP
- Christoph Pfurtscheller, Infrastructure Engineer, Core Services, BWIN
Slides from original presentation.
SCOM 2019: What's next
System Center releases
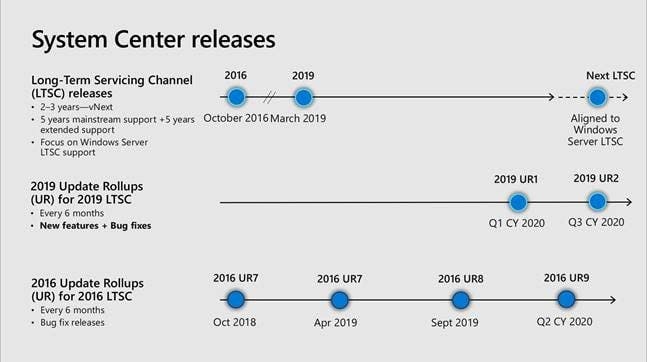
Some really good news right at the front of the presentation, the Semi-Annual Channel (SAC) release schedule is gone for good! For those of you who didn't make the jump, after the 2016 version, Microsoft was going to release a new version every six months or so. Each of these releases had a different support life-cycle. While I was initially excited about this more aggressive release cycle, the reality was that it caused more problems for everyone. Also announced was five years of mainstream support, plus five years of extended support for the Long Term Servicing Channel (LTSC) which is also aligned with the Windows Server LTSC. It is my belief that the 10-year support life-cycle was always true, but I also believe that it wasn't widely known, so announcing it publicly should have reaffirmed desire for hybrid (on premises and cloud) monitoring. Lastly, the first Update Rollup for the 2019 release will be released in January.
SCOM and Azure: better together

Speaking of Microsoft's updated monitoring message, Vithalprasad explicitly called out several cases where having System Center AND Azure in your data center is the appropriate solution, as opposed to having one OR the other. Personally, I think this stems from Microsoft's attempt at reframing the monitoring message with this year's Ignite. Thinking back to past conferences, blog posts, and the Operations Management Suite (OMS, which was pre-Azure Monitor) there was an obvious effort to move everything from on premises to the cloud regardless of appropriateness or cost. While outside the scope of this particular blog post, there were numerous sessions where Microsoft is reframing their message to be more "encompassing" to the whole community.
System Center v Windows Admin Center
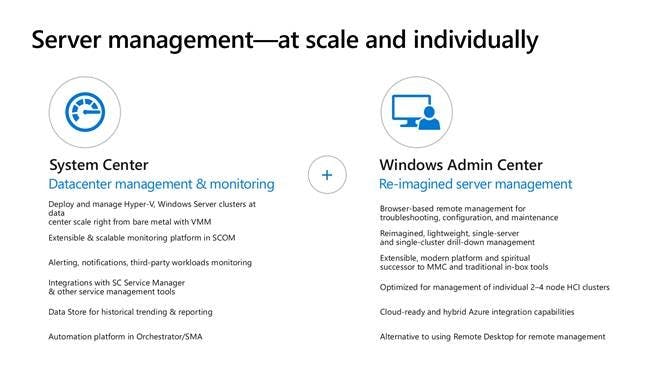
Another excellent (but too short) message for the IT Pro is that you should choose the right tool for the right job! What I'm referring to here is the difference between System Center and Windows Admin Center. Vithalprasad presents an excellent case where each tool is positioned in its own space.
“Alert Closure Failure” feature
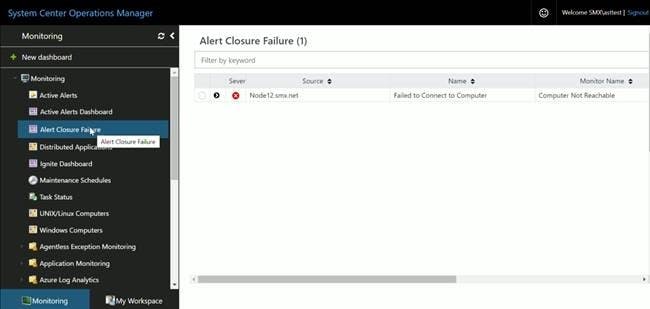
Above: The "Alert Closure Failure" dashboard in the HTML console
Now to the new features! Well, how about a semi-new feature? Um, how a feature from last year…? All kidding aside, this is an excellent new feature for SCOM 2019. By itself, this feature alone should convince the SCOM Admin to upgrade to the next version. It's good to see that Microsoft is still pushing this because it really is a game changer (and something that should have been in the product years ago). My only complaint is that the "Alert Closure Failure" node is ONLY visible in the HTML console, not in the console.
Monitoring Storage Spaces Direct
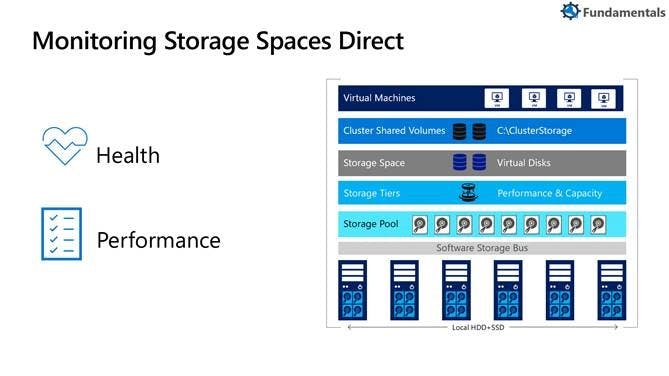
Has anyone tried the original Storage Spaces Direct management pack? I did. It wasn't very good (at least in my opinion and in my previous shop). On the other hand, this updated pack looks very promising! In fact, it looks so promising, I wonder (and hope and pray) that Microsoft will update the Hyper-V packs so that they can visualise that technology stack in the same way they're visualizing the S2D stack.
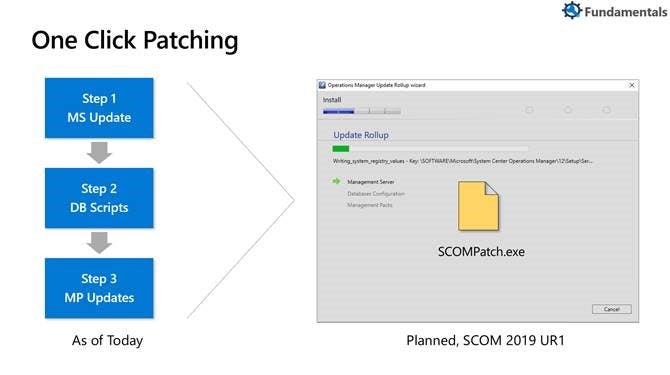
One Click Patching
Here's a new feature targeted squarely at the SCOM Admin: one-click patching! Starting with SCOM 2019 UR1, when you click on one-single file, your SCOM landscape will get updated. While there is precious little information about this feature in the wild yet, but according to some of the Q&A answers we received at the end of the presentation, even the Gateway servers will get updated by this process. Part of me is really excited by this new process, but my other half thinks this might not be a good thing… I guess the devil will be in the details… Looking forward, if it really is as flawless as I think they want it to be, this could be really good for SCOM Admins to keep their landscape up-to-date.
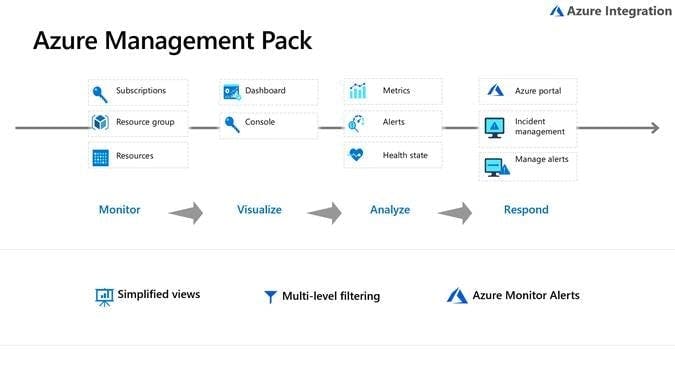
Azure MP
I never had a chance to work with the original SCOM Azure pack. I've heard that it was hard to set up and get working and that sometimes it would stop working (and not throw an alert). I've connected my SCOM landscape to OMS (which morphed into Azure), but I've never actually monitored Azure. I'll have to set up a test landscape to really kick the tires on this.
Support for Group Managed Service Accounts (gMSA)

Here's a feature that many security teams are dancing in the isles for! If you're not familiar with Group Managed Service Accounts (gMSA's), they're a really neat feature of Active Directory that changes the password for your service accounts automatically. Essentially, when you implement a gMSA service account, changing the password every 30/60/90 days becomes a thing of the past. However, while I never had to configure a SCOM landscape with gMSA, I have used gMSA's for SQL Server in the past, and it was a nice trick to log into the server with the Service Account to test a scenario or track down an issue. With gMSA's, that ability is now gone… So, if you're using your SCOM service accounts in a bunch of crazy places (like a scheduled task or something else), get ready for some headaches as you make the transition.
Distro-agnosic MP
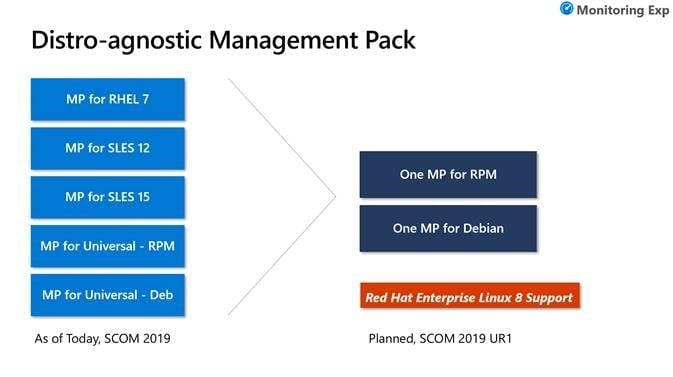
Ah, Linux. This is one feature that I am VERY glad to see on the horizon. Recently, due to escalating costs, our entire shop at my previous outfit switched from RHEL to Oracle Linux. Since each Linux distro required a different management pack, all of my agents went gray. I needed to add the new Oracle Linux management packs, work with the Linux team to remove the agents (because for whatever reason, I couldn't just rescan the agent), and then perform fresh discoveries of our entire Linux server farm. Needless to say, that was A LOT of effort. My hope is that that scenario will become a thing of the past with this update…
There was also some talk about older Linux distros not being supported going forward. I'm not sure of the impact of that yet, but I don't see why you couldn’t have the older packs installed alongside the new packs. I guess we'll know more once the Update Rollup is released…
Customer stories
As mentioned earlier, there were also two customer stories presented in-line with the SCOM features. The first presentation was by Petr Volprecht, Global Service Owner for SCOM at SAP and Christoph Pfurtscheller, Infrastructure Engineer for Core Services at BWIN.
The SAP presentation included a nice slide detailing the SCOM landscape, which I think is always refreshing to see since a lot of Admins don't scale out enough for SCOM. Another interesting aspect of the SAP presentation was how they used Microsoft's SharePoint and React to create a pseudo-self-service portal for SCOM monitoring. The second presentation from BWIN focused on their very distributed SCOM landscape with Gateways (which are really underutilized in my opinion). A highlight in this presentation was the agent-initiated maintenance mode, but not enough information was shared. Personally, I really like when Microsoft highlights these enterprising SCOM Administrators, but it would be grand if they would be given more time to focus on the technical details of their infrastructure and on some of the third-party tools they use to really make SCOM shine.
At the end of the presentation, Hitesh and team took questions, which was also very refreshing and enlightening!
Here are some additional references:
- Want to influence the next version of SCOM?
- SCOM 2019: Customer Success Stories and What's Next
- System Center Operations Manager User Voice