The Big SCOM Survey: Full results
Below is the full list of results for the Big SCOM Survey. We surveyed 118 SCOM users with 27 questions.
For the key highlights and expert analysis of these results head over here.
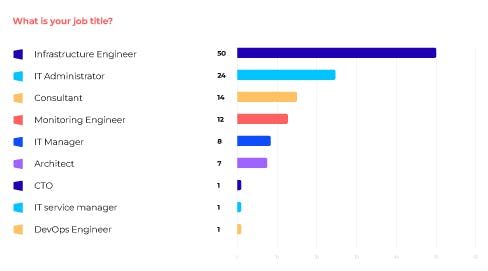
Our respondents mainly consisted of Infrastructure Engineers (42.4%), IT Administrators (20.3%), Consultants (11.9%), Monitoring Engineers (10.2%) and IT Managers (7.8%).
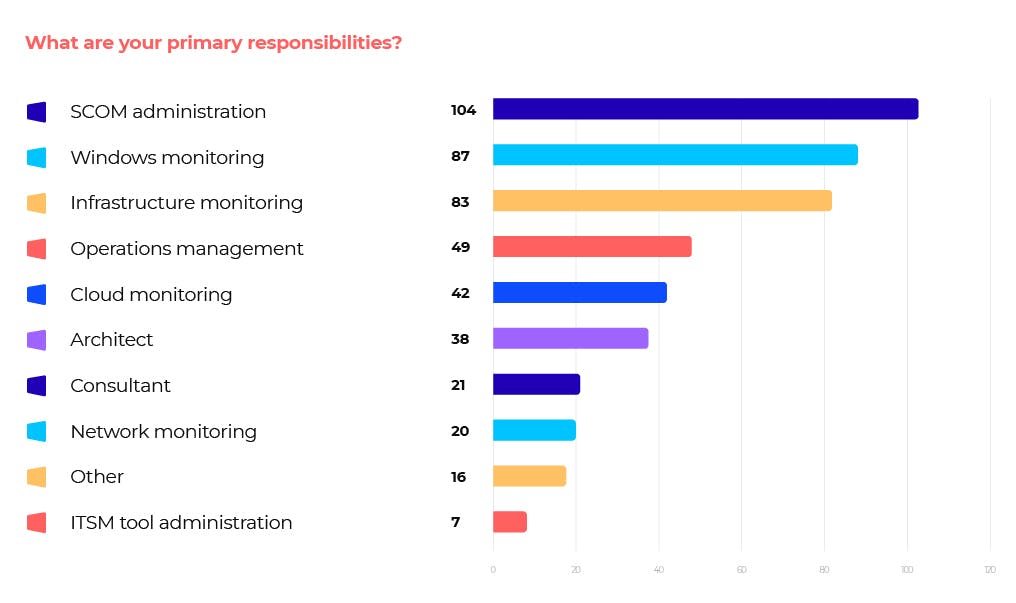
The majority of respondents (88%) have ‘SCOM administration’ as one of their primary responsibilities. The next most popular answers were ‘Windows monitoring’ (73.7%) and ‘Infrastructure monitoring’ (70.3%).
35.5% selected ‘Cloud monitoring’ and 41.5% ‘Operations Management'.

34% of respondents have been using SCOM for 7-10 years, and 25% have used it for 11-15 years. Roughly 10% have picked it up in the last 3 years.
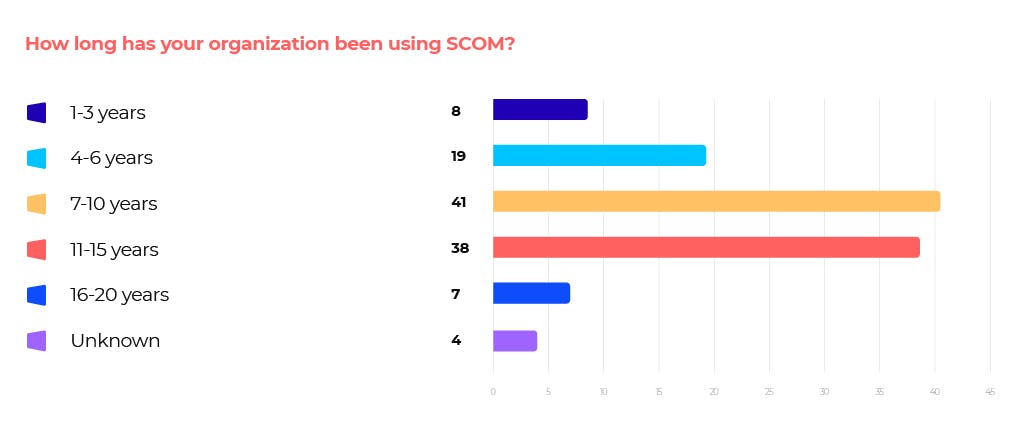
The organizations represented have been using SCOM for a similar amount of time to the respondents surveyed, with 35% using SCOM for 7-10 years and 33% using it for 11-15 years.
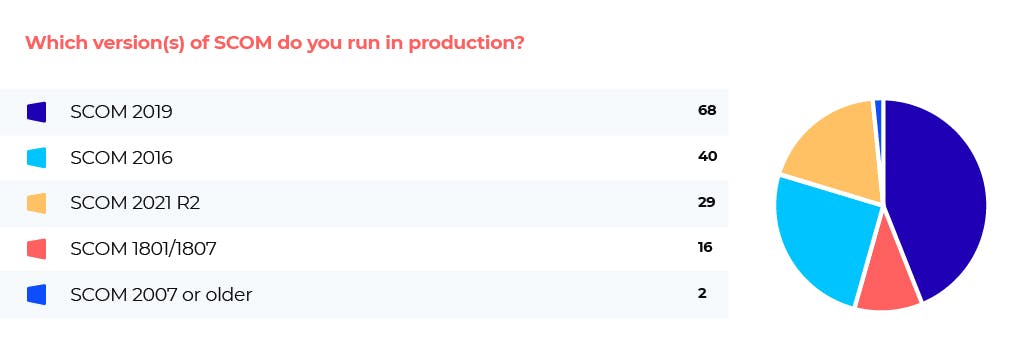
57.6% of respondents run SCOM 2019, while 33.9% run SCOM 2016 and 24.6% run SCOM 2012 R2.
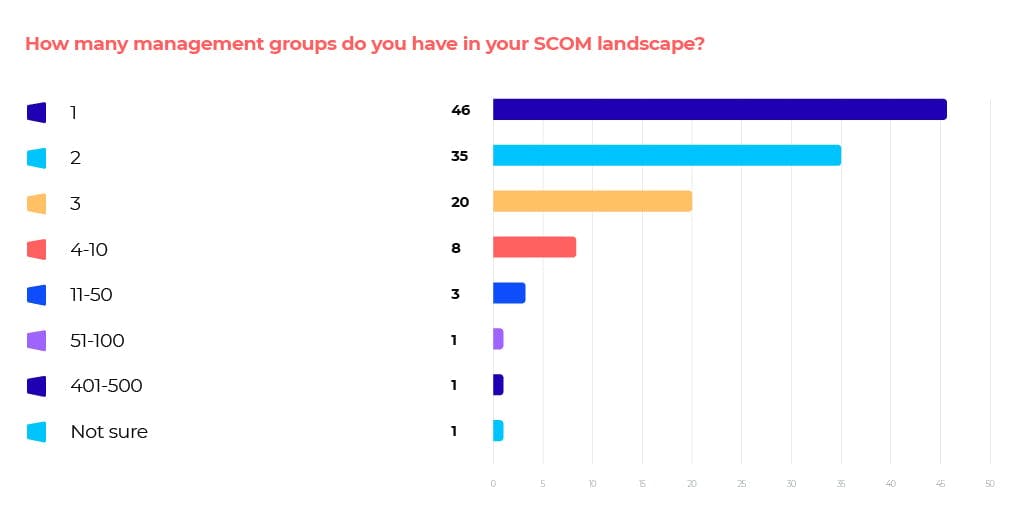
The majority of respondents (40%) have just 1 management group, while 30% have 2 and 17% have 3.
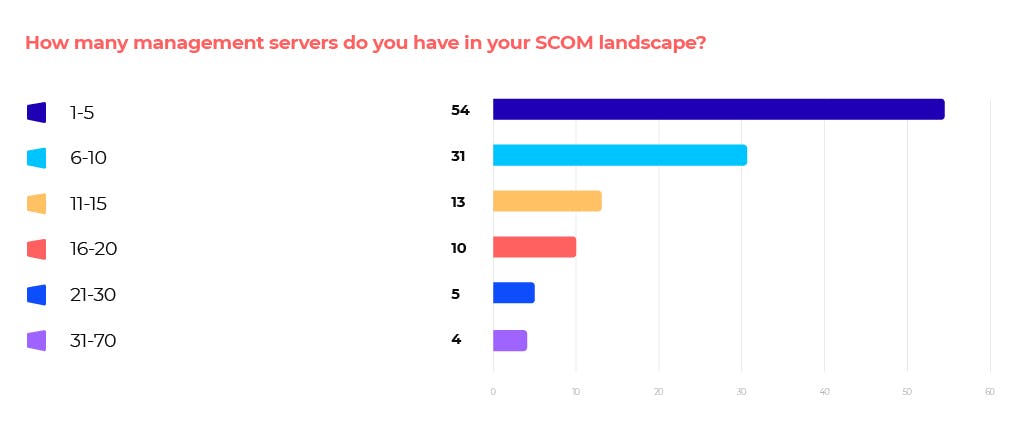
The majority of respondents (46%) have 1-5 management servers. 26% have 6-10, while 11% have 11-15. Approximately 9% of respondents have more than 20 management servers.
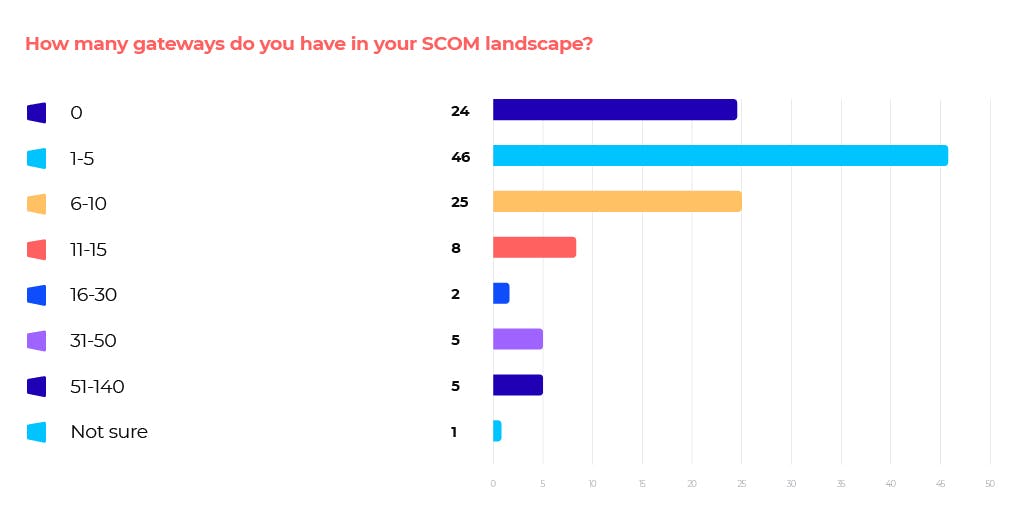
A significant number of respondents do not have any gateways (20.7%). 40% have 1-5, while 22% have 6-10.
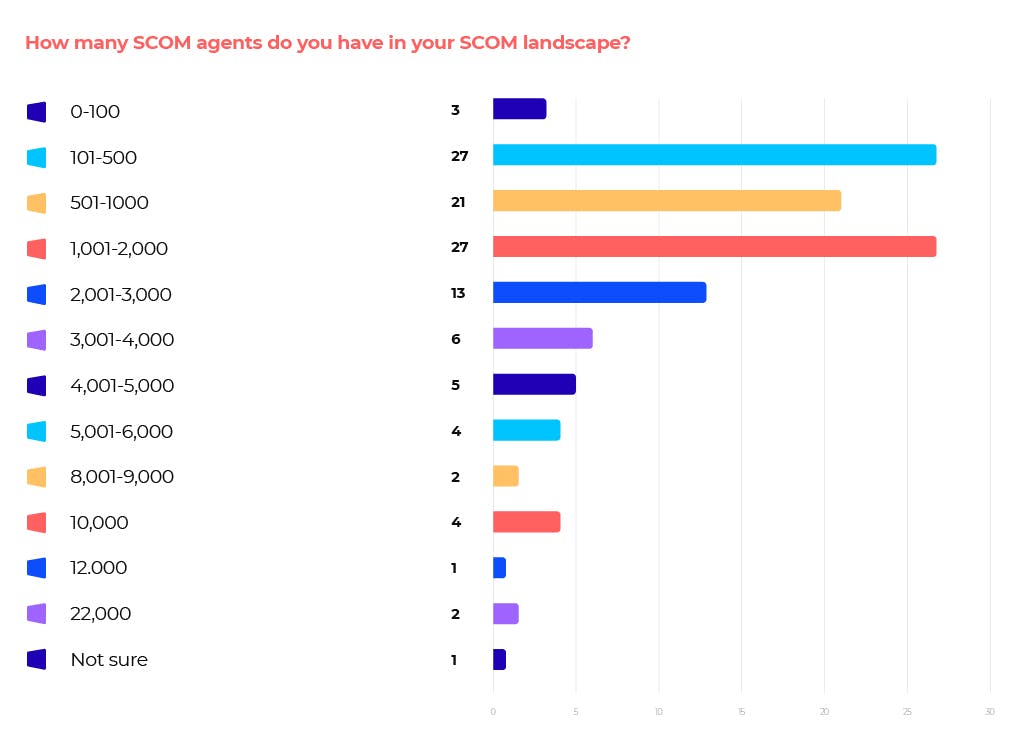
The number of SCOM agents that respondents have varies widely, with 76% of respondents indicating between 100 and 3,000 SCOM agents.
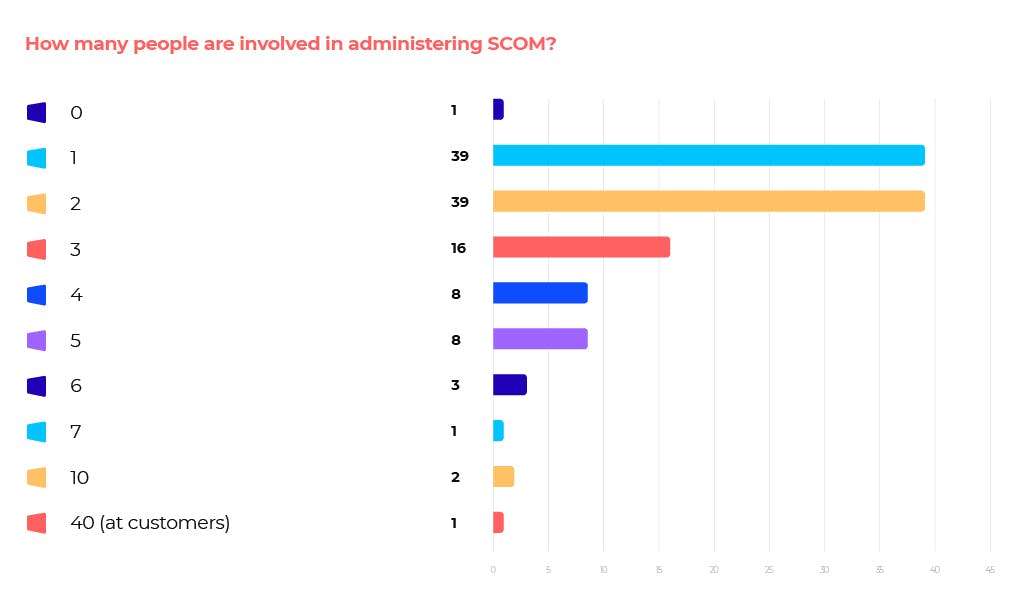
The majority of organisations (66%) have 1-2 people involved in administering SCOM.
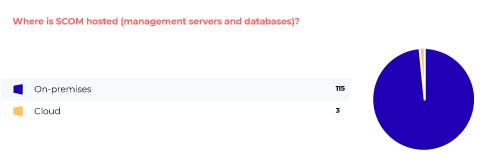
97.5% of respondents have SCOM hosted on-prem.
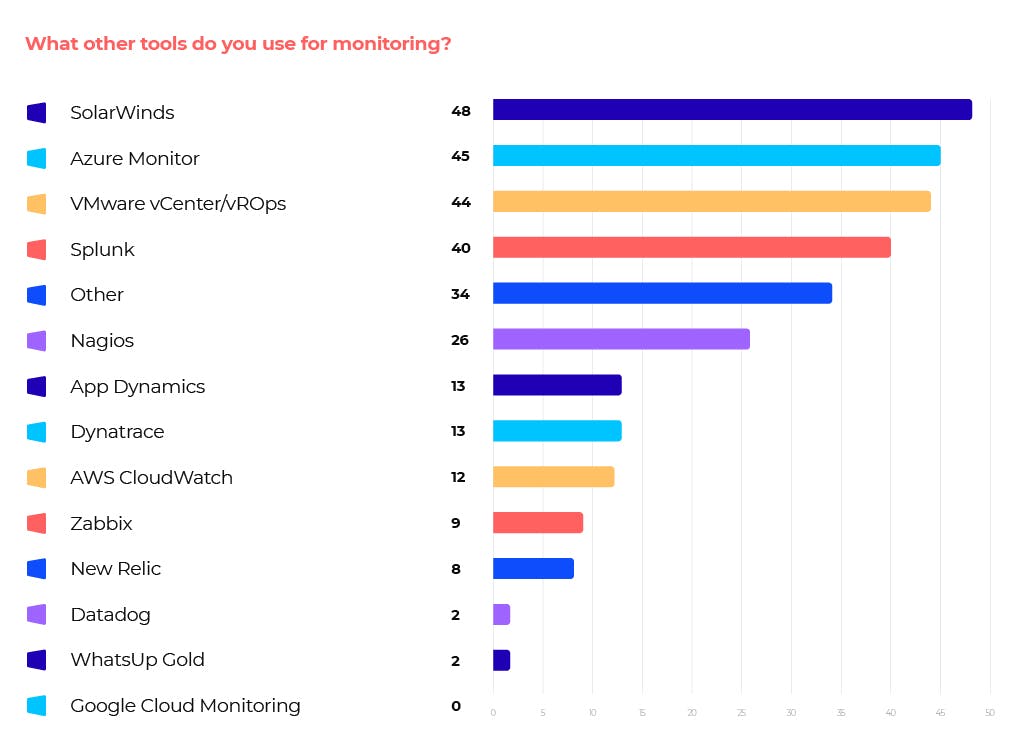
These are the four most popular tools outside of SCOM among our respondents:
40.7% of our respondents use SolarWinds, 38.1% use Azure Monitor, 37.3% use VMware vCenter/vROps and 33.9% use Splunk.

The most popular Management Packs are Veeam for VMware, F5 Big IP, Citrix SCOM MP and OpsLogix (specific MP not provided).
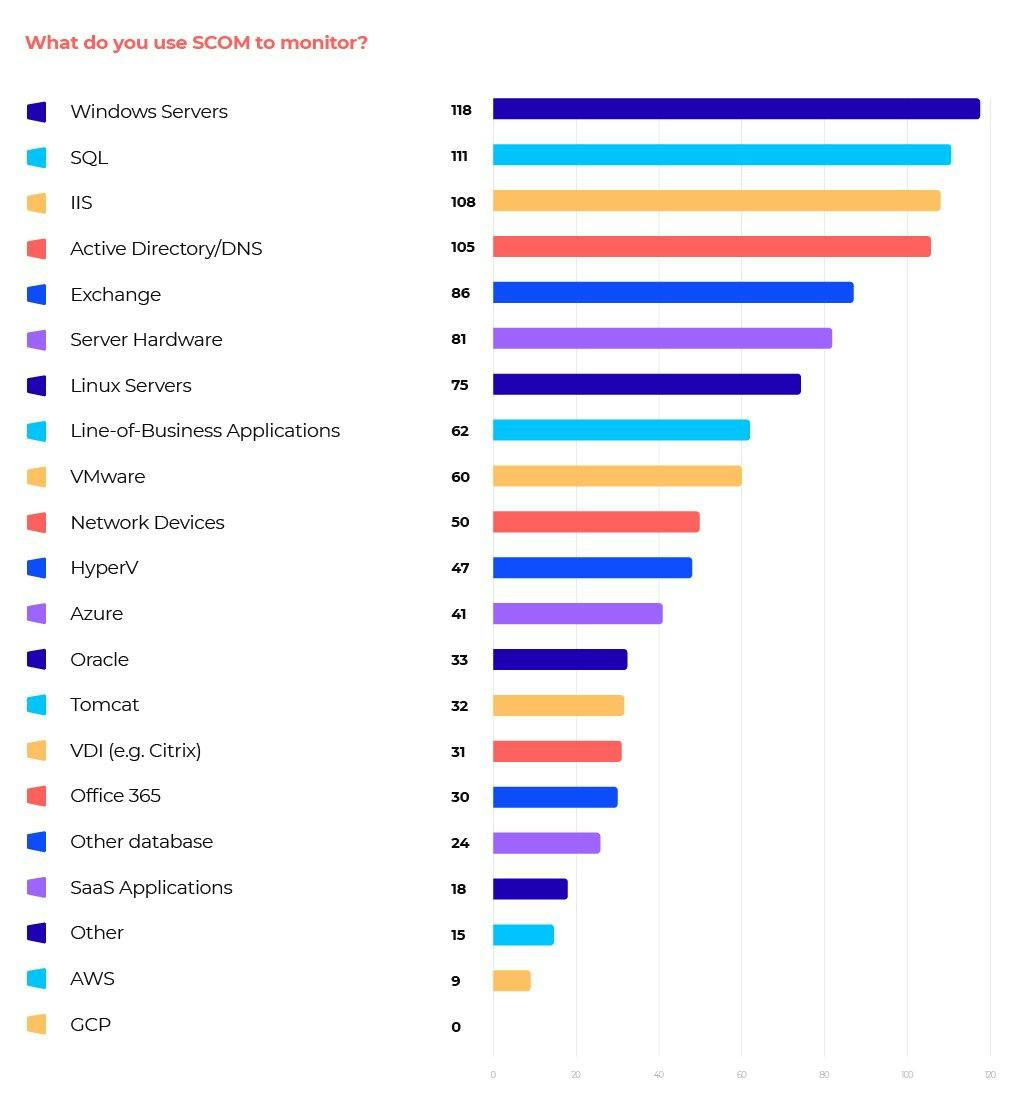
SCOM is most often used to monitor Windows Servers (100%), SQL (94.1%), IIS (91.5%), Active Directory/DNS (89%) and Exchange (72.9%).
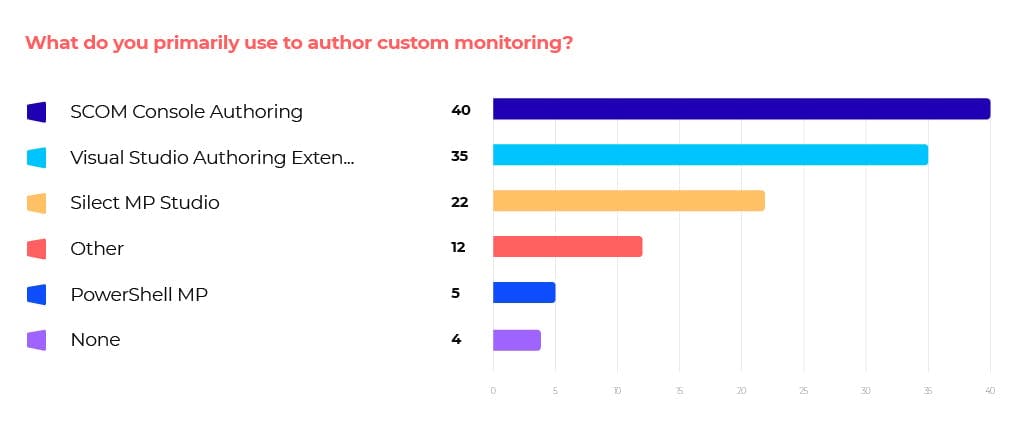
SCOM Console Authoring (33.9%) is the most-used tool for authoring custom monitoring, followed by Visual Studio Authoring Extension (29.7%) and Silect MP Studio (18.6%).

Most people primarily use custom MPs for additional rules and monitors (52%). This is followed by Monitoring Application Specific Components (24%) and Monitoring Additional Platforms/Technology (20%).
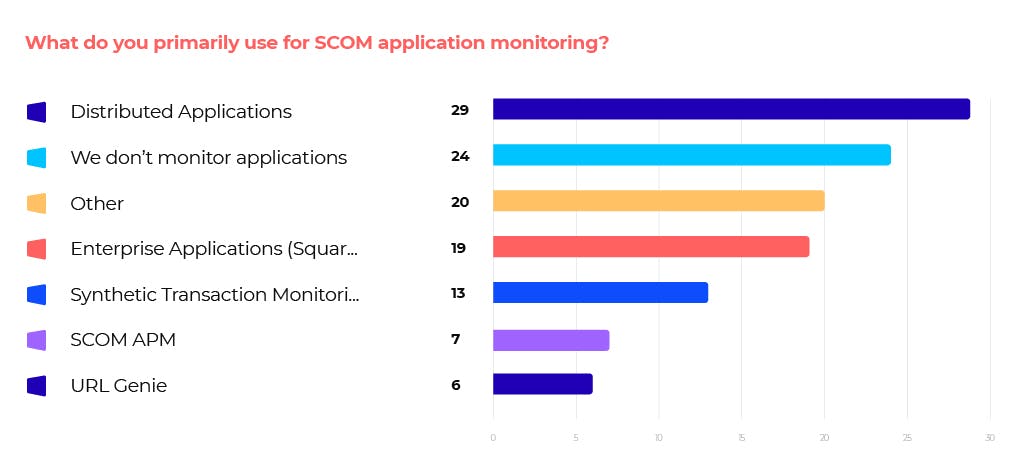
25% of respondents use Distributed Applications for SCOM application monitoring, while 16% use SquaredUp’s Enterprise Applications feature. 20.3% do not monitor their applications at all.
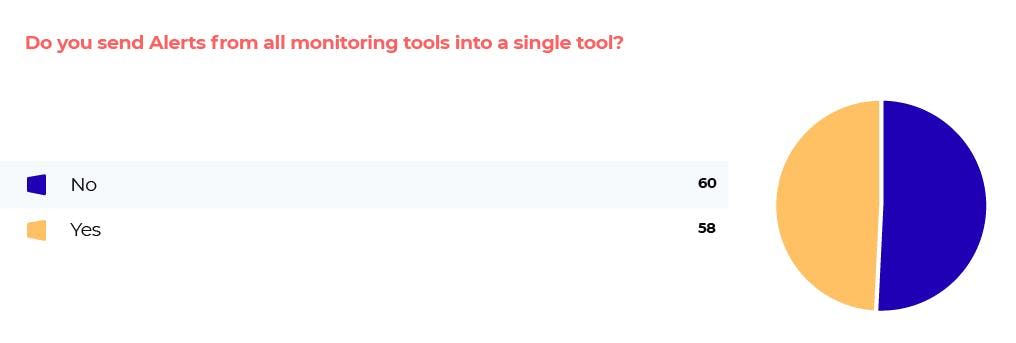
51% send alerts from all monitoring tools into a single tool, while 49% do not.
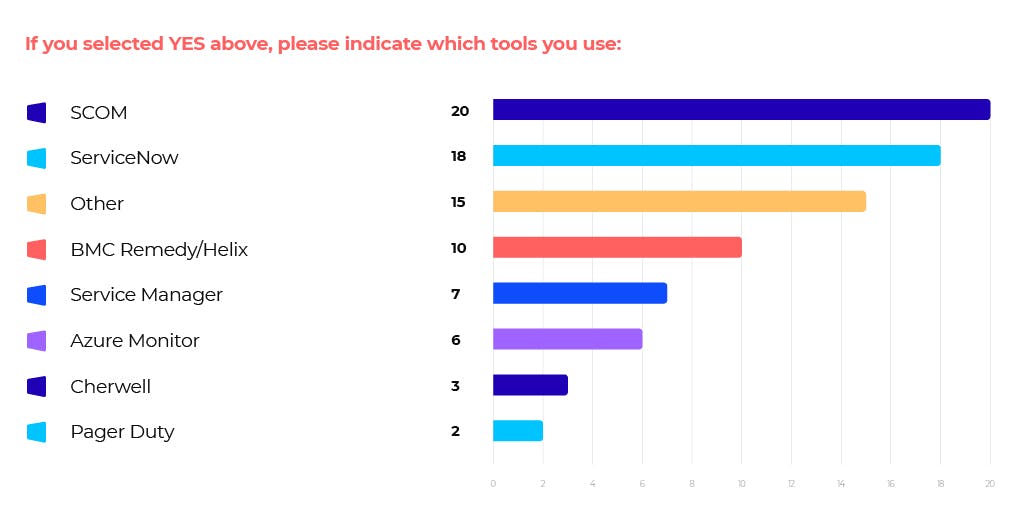
Of those who do send their alerts into a single tool, these are the top tools they use:
- SCOM 33%
- ServiceNow 30%
- BMC Remedy/Helix 17%
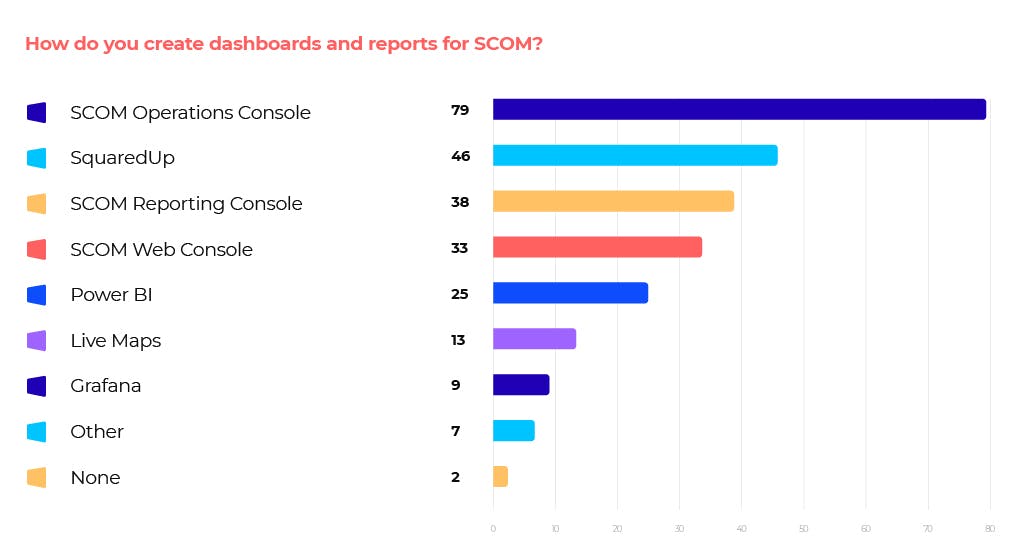
67% of respondents use the SCOM Operations Console to create dashboards and reports for SCOM. 39% use SquaredUp, 32% use the SCOM Reporting Console and 28% use the SCOM Web Console.
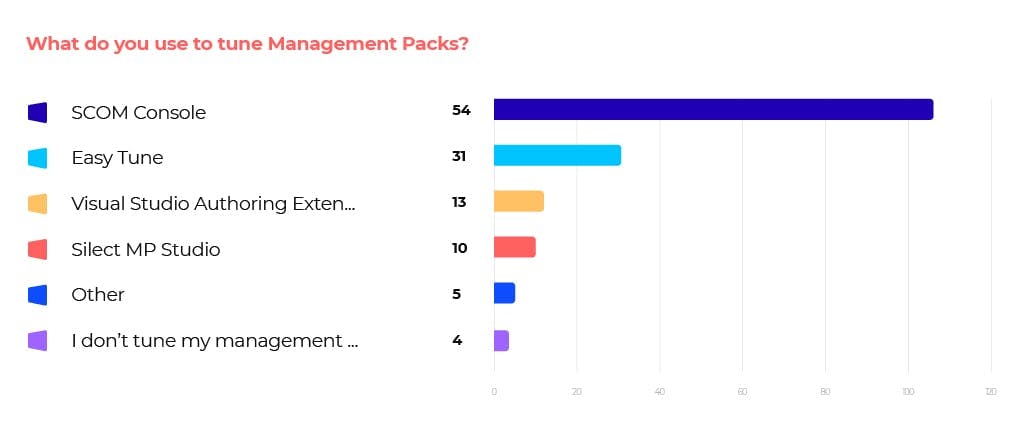
The vast majority (90%) use the SCOM Console to tune management packs. 19% use Easy Tune and 18% use Visual Studio Authoring Extension, with 2.5% indicating that they do not tune their MPs.

While cloud use has gone up, the majority of respondents (61%) expect their SCOM usage to increase over the next year. 35.6% expect it to stay the same, and only 8% expect a reduction.
We also asked respondents to explain their answers (Grow, Stay the same, Reduce):
Answer: Grow
- Because we have not yet really looked at other tools, plus we need to consolidate some of our toolsets.
- I'm steadily introducing all of our business services
- Internal and cloud expension
- Hybrid Cloud based Infrastructure with a lot of investment into SCOM. We are enabling monitoring of Cloud via Azure & O365 management packs.
- As we are using SCOM as more of a Data source for integrations where we can, so SU can be the single pane
- As SCOM also will be used for Azure Cloud Apps monitoring & bringing in more custom monitoring for In-house Apps of the customer
- expand usage to monitor resources in Cloud and other devices/apps
- More and more benefits on APM
- We are in a journey that will move big number of servers from on preem to cloud, this will raise the control of monitoring new resources.
- We are in the process of migrating a substantial percentage of our onprem environment to the cloud. We have found native cloud monitoring services to provide less functionality at an increased cost. We are not only a SCOM shop, but an SCCM shop as well, and since they share the same client MLs, SC licensing is essentially a sunk cost.
- We continue to add more servers in our environment
- We are always introducing new monitors into SCOM.
- Squared Up is driving the desire for monitoring, people like to see fancy dashboards! Every new service that we release needs monitoring, which wasn't the case before I setup SCOM.
- Extending monitoring to more servers and more MPs e.g. DHCP
- increase in custom monitoring
- Because there is an increasing number of demands from Business departments to monitor mode business applications
- Resource growth in Azure and GCP
- We are planning on upgrading to 2019 and to use the SCOM 2019 to monitor our future deployment of Windows Server 2019 servers.
- We expect to grow SCOM via engaging more Application owners within the organization, as well as adding Azure monitoring tools for our cloud presence. Also would like to see Linux systems integrated.
- Its our go to monitor and as we grow skills and use PowerShell more, its reach is ever greater
- We are migrating from other monitoring tools
- Looks like MSFT is finally giving more love to SCOM (again) and customers feel that.
- New Technologies and a consolidation of monitoring toolsets are coming. SCOM is, by far, the easiest to integrate with ServiceNow.
- (1) solid monitoring platform, (2) microsoft has this product still on their roadmap, (3) extendable via the concept of MPs
- There is a growing awareness and recognition that SCOM is not as bad as its reputation, and it is indeed a very capable and feature rich product that still has support at Microsoft. SCOM has much more support from 3rd parties, SquaredUp, Silect, CookDown, etc. etc. than it has ever had.
- Extend with the Azure MP after updating SCOM
Answer: Stay the same
- Without any proper training or any investment to purchase 3rd party apps to help SCOM grow I don't believe that our SCOM environment will change very much
- Currently other applications are being reviewed
- Happy with SCOM
- Monitoring needs are increasing considerably, but in areas where SCOM is not best of breed
- Hybrid environment for some years to come
- It is not the tool which is accepted from the people in my company
- We are slow to change
- It is difficult to engage other teams to build more robust monitoring of their applications and systems. I don't expect that to change.
- Transitioning to the cloud in the next 5 years
- We do not expect many new on prem servers and we do not monitor the cloud with it.
- SCOM mostly used for internal infrastructure, which tends to be stable.
- I would love to increase it, but lack of “monitoring as code” options prevents that
- What we will add in components etc, will be lost for SCOM by implementing Dynatrace.
- Mature product and the company do not seem to be adding new servers at the moment and we are looking at cloud solutions.
- I have had a lot of difficulty when trying to engage most of our teams to build monitoring for their applications/systems. I don't expect that anything will change any time soon.
- No environment growth
- The number of servers we have remains about the same, but we are migrating to Azure. Right now Azure monitoring tools are not on a par with SCOM so any server in Azure still has a SCOM agent. In coming years as we use more SaaS and PaaS in Azure I can see less reliance on SCOM but until we have so few servers (on-prem and Azure) that doesn't make SCOM worthwhile and/or Azure monitoring tools get better we will stay with SCOM.
- Stablity
- No investments in infrastructure.
- There's a push to use Azure Monitor for more monitoring as we have recently been through a cloud migration process. However, there's still a number of services on-prem so it will still be used.
- We are just starting our journey into to the cloud (this time for real) so we are not sure how much on prem we are going to have in the future.
- Well with the focus on azure or cloud. I would expect a decrease or the same. But I hope that SCOM will grow continously from the help from MS, squared UP, and community to keep it growing.
Answer: Reduce
- company moves many services on the cloud, and have to use different monitoring tools. But I doubt that we will decommission SCOM soon
- Systemcenter will be removed from our Organisation. --> License Cost ( SPLA) .
- More thing are moving to the cloud. Limitations on what scom can monitor on the cloud
- SCOM is perceived end of life; very limited cloud monitoring without big expenses in 3rd party MP's, IT is getting easier, but SCOM is not.
- SCOM is very limited and not very versatile when it comes to setting up good Monitoring. Very complicated and convoluted to comprehend limitations of using Groups, applying overrides to which Targets and when etc.
There are no easy way to Customise Alert description Test for Alerts on the Console.
There are no Android or iOS Apps available to capture and view alerts on portable devices such as mobile phones.
Network monitoring is is totally useless.
SNMP monitoring is hopeless. - no new mps and still not getting all the mps like pure storage, rubrik
- Microsoft doesnt do the best for SCOM, just for Azure Monitor. Poor visualization, poor APM features, no ML and AI
- We don't use SCOM to monitor Azure servers typically so as more migrates to Azure SCOM may reduce. Not sure yet
- It looks like our clients are moving either to Azure Monitor or Splunk
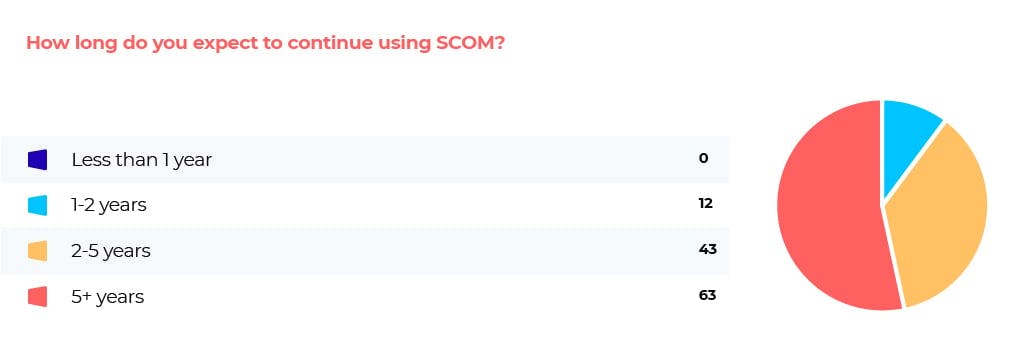
The vast majority of respondents (90%) expect to continue using SCOM for over 2 years. Just over half (53%) expect to continue using it for 5+ years, while 36% expect to continue using it for 2-5 years more.
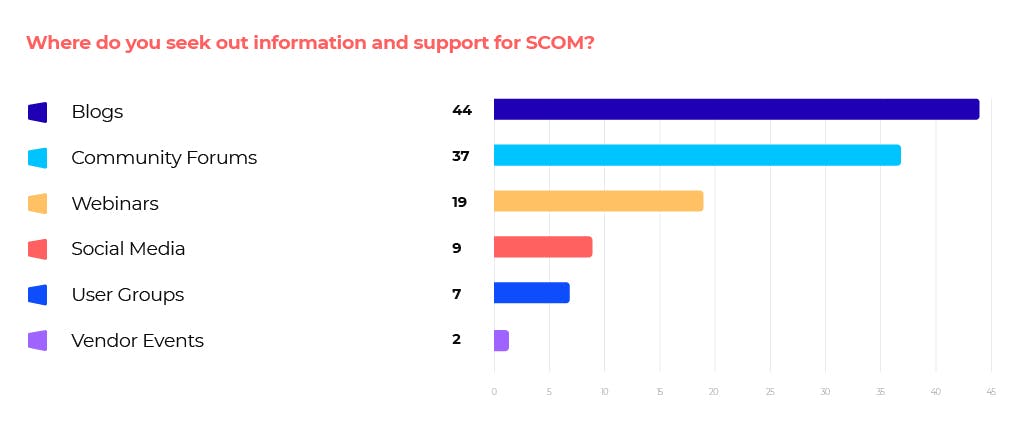
The majority of respondents seek information and support for SCOM via blogs and community forums, with 37% turning to blogs and 31% community forums.
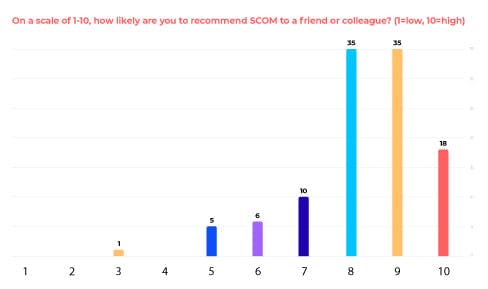
80% of respondents rated between 8 and 10.
Average number 8.25
What additional features would you most like to see added to SCOM?
List of responses:
- Easier custom authoring, especially for custom classes and discoveries
- Automatic health watcher for groups
- Certificate Monitoring
- Context for all events
- Unification of SCOM and Azure Monitor
- ADFS Login synthetic transaction monitoring
- Native Web API support with wizard driven setup
- Modern consoles for operations and administration
- Capacity management
- Auto topology mapping
- AI/ML driven alert tuning
- Ability to raise Alerts when multiple conditions are met (like time, proximity, similarity)
- Different overrides for different times of day/days of the week
- Faster experience
- Auditing of customisations and overrides
- Improved/modernised dashboards (natively)
- Easier alert tuning and overrides
- Improved native O365 monitoring
- SCOM as a service
- Better Cloud integratiom/Monitoring MPs
- Improved/modernised reporting
- APM features
- Auditing of maintence mode
- Customisable alert descriptions
- Audible notification of new alerts from console
- Mobile app for viewing alerts
- Improved Network monitoring
- Alert correlation to supress alert storms when a dependant component is down (eg top layer Network Router/Switch fails)
- Improved SNMP monitoring setup and reliability
- Ability to create groups from a file (eg CSV)
- Ability to add metadata to objects from SCOM console
- Wizard to create classes from registry keys
- Mobile app for SCOM administration
- SNMP v3 support
- Native synthetic transaction monitoring
- Native SaaS custom app monitoring
- More granular role based access controls
- Container monitoring
- Wizard to create alerts from Log Analytics (as with Windows Events)
- Option to import MPs with monitoring disabled by default to allow me to only enable monitoring required
- Edge/Chrome support for Web monitoring and APM functionality (instead of IE11)
- More MPs that add monitoring capabilities and are supported
- Salesforce Integration
- xml schema documentation
- Unify how Unix agents communicate with SCOM to match Windows
- Make all Linux/Unix MPs universal so new versions are supported as they are released and to allow support for a broaded range of Linux variants
- More native cloud monitoring
- Support for Azure SQL for SCOMs Databases
- Better best practice guidance for management
- Group reporting for perf counters
- Better integration with Azure Monitoring tools
- Better website monitoring
- Better log monitoring, discovery and health
- Improved sample reports
- Add PowerShell support to Maintence mode scheduler to allow other things to be scheduled in SCOM
- Improved group creator experience
- Improved notification channel subscriptions to allow exceptions (EG alert if A but not if a member of group B)
- Native integrations with more third party prodcucts like ServiceNow, BMC and Slack
- Vunerabiility monitoring natively
- Native database and powershell support when authoring monitoring
- Agentless Linux monitoring