Using SCOM to detect missing Active Directory site IP subnet allocations

We say hello to Ruben Zimmerman today for his first guest post on our blog. Ruben is an infrastructure specialist, who specializes in Active Directory, public key infrastructure and System Center Operations Manager (SCOM). Ruben has written an article on how to use SCOM to detect missing Active Directory site IP subnet allocations - let's get started.
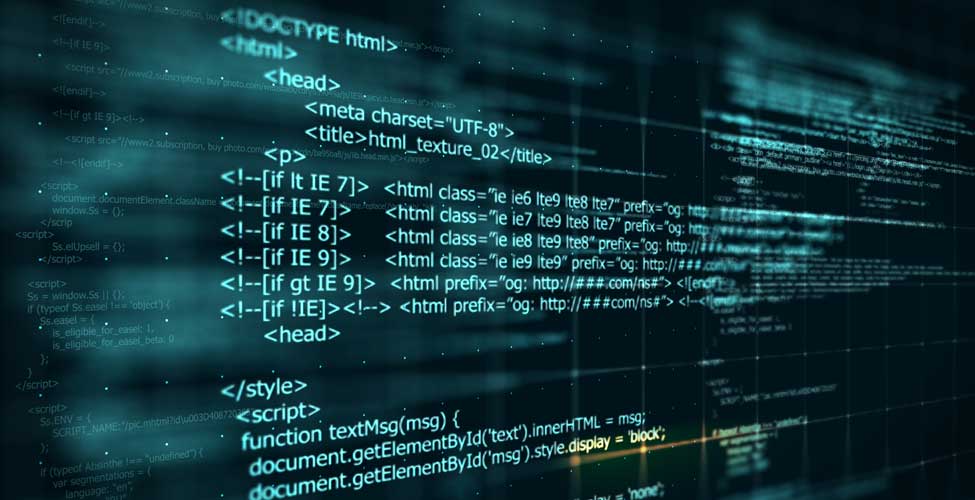
PowerShell script to parse netlogon.log
Crucial for our script is the log file netlogon.log located in C:\Windows\debug\ that contains information about clients with missing subnet allocations. A typical record could look like this:
04/08 16:11:14 Contoso: NO_CLIENT_SITE: Wks-01127 10.20.12.34
Month/Day Hour:Minute:Second AuthenticationTarget NO_CLIENT_SITE ClientName ClientIPThe following script parses the log file and stores all entries of the current day in a list. If there is an entry in the list, it will send the overthreshold state to SCOM and underthreshold if not.
$scomAPI = New-Object -comObject "MOM.ScriptAPI"
$propertyBag = $scomAPI.CreatePropertyBag()
$computerName = $env:COMPUTERNAME
$cleanedList = New-Object -TypeName 'System.Collections.Generic.List[psobject]'
$uniqueList = New-Object -TypeName 'System.Collections.Generic.List[psobject]'
try {
$logContent = Get-Content -Path C:\Windows\debug\netlogon.log
$noClientSite = $logContent -match 'NO_CLIENT_SITE'
$today = Get-Date -Format 'MM/dd'
$todaysRecords = $noClientSite -match "$($today).*"
foreach ($record in $todaysRecords) {
$recordItems = $record -split '\s{1}'
$itmDate = $recordItems[0]
$itmAuthTarget = $recordItems[2]
$itmClientName = $recordItems[4]
$itmClientIP = $recordItems[5]
$recordHash = @{'DomainController' = $computerName}
$recordHash.Add('Date', $itmDate)
$recordHash.Add('AuthenticationTarget', $itmAuthTarget)
$recordHash.Add('ClientName', $itmClientName)
$recordHash.Add('ClientIP', $itmClientIP)
$recordObj = New-Object -TypeName psobject -Property $recordHash
$null = $cleanedList.Add($recordObj)
}
$cleanedList | Sort-Object -Property ClientIP -Unique | ForEach-Object {
$null = $uniqueList.Add($_)
}
$messageText = "The following computers could not find a DC that matches their IP range and where authenticated against $($computerName) `n`n"
$messageText += "Please map the IP ranges to Sites in the Active Directory Sites & Services MMC. `n`n"
foreach ($client in $uniqueList) {
$messageText += "Client Name: $($client.ClientName) `t, Client IP: $($client.ClientIP) `t Authentication Target $($client.AuthenticationTarget) `tDate: $($client.Date) `n"
}
} catch {
$messageText = "Failed to parse logfile with error message $($error)"
}
$propertyBag.AddValue("MessageText",$messageText)
$propertyBag.AddValue("ComputerName",$computerName)
if($uniqueList.count -gt 0) {
$propertyBag.AddValue("Result","OverThreshold")
} else {
$propertyBag.AddValue("Result","UnderThreshold")
}
$propertyBagApplication Performance Management
Your complete guide to the latest IT monitoring trend
Creating the SCOM alert rule
With the help of our PowerShell script, we can now create a new SCOM rule. In the SCOM Management Console, switch to the Authoring pane, expand Management Pack Objects, and right-click on Rules. Choose Create a New Rule. Expand Alert Generating Rules and PowerShell Based. Select PowerShell Script Alert Generating Rule (Community), and click on New to create new management pack (MP) to store the configuration in.

Use a descriptive name for the management pack, such as ActiveDirectory.Custom.RulesAndMonitors. This helps keep an overview of MPs.

Optionally, maintain additional content as part of the knowledge component of each MP. Proceed by clicking on Create.

Back in the rule wizard click on Next to proceed with rule authoring.

Enter a rule name such as Discover Active Directory Missing IP Range <-> Site Allocations, a description, and choose the rule target. The rule target defines on which computers the rule will execute. In our case it must be the Windows domain controller.

In the Schedule section choose twice a day for example.

In the Script section choose a file name, for instance, Parse-NetlogonLog.ps1. Set the timeout to two minutes and paste in the script from above. Proceed with Next.

Keep the Criteria section unchanged and proceed with Next.

Lastly, configure the alert with a severity of Warning and the Alert description containing a least the following information:
$Data/Property[@Name='MessageText']$
Creating a new alert view
Next, we have to create a new alert view about missing IP subnet allocations.
Change to the Monitoring pane, right-click the ActiveDirectory.Custom.RulesAndMonitorscontainer, and select New –> Alert View.

Name it Missing IP Range <-> Site Allocations for example. Specify the target Windows Domain Controller and filter it to show only those alerts with the string %Active Directory Missing IP Range%.

After a while, all domain controllers will have downloaded the management pack. This screen will show the first alerts.

We hope you enjoyed this article by Ruben. Keep a look out for his next guest appearance soon!